
Any organizational growth implies complexity. One common approach is to reduce some of the workload of access management with Azure Active Directory (AD) admin roles. One of the ways how you can delegate administrative roles is Azure Active Directory Administrative Units.
Assigning least possible administrative privileges to users. As result of that, they can access their applications and do their job.
Centralized or delegated permissions?
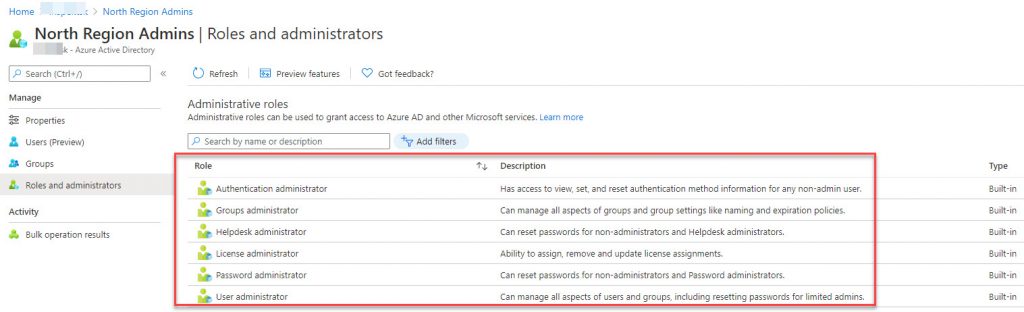
As an organization grows, it can be difficult to keep track of which users have specific admin roles. Attackers who get control of privileged accounts can do tremendous damage. Azure has certain Baseline Polices, that enable protection. This policy enforces multi-factor (MFA) authentication on privileged Azure AD accounts. Azure AD roles covered by this policy are:
- Global Administrator
- Groups Administrator
- Helpdesk Administrator
- License Administrator
- Password Administrator
- User Administrator
How many administrators you have and how granular their permissions are, closely relate to the size and complexity of the environment. The scenarios are:
- Small proof-of-concept (PoC): one or few administrators do everything. In this case, each one of them is assigned Global Admin role.
- Larger deployment with more machines, applications and desktops: several administrators have more specific functional roles. For example, some could be Application Administrators, Security Administrators.
- Enterprise deployments: complex, hybrid environment will require more granular permissions, as well as some unconventional or hybrid assignments.
As a result of this, developing delegating model that fits your needs is important. Recommended steps for this, would be:
- Define the roles you need
- Delegate app administration
- Grant the ability to register applications
- Delegate app ownership
- Develop a security plan
- Establish emergency accounts
- Secure your administrator roles
- Make privileged elevation temporary
More info: Azure Active Directory Roles delegation
What are Azure AD Administrative Units?
It is an Azure Ad resource that serves as container for other Azure AD resources (only users and groups). Administrative units restrict permissions in a role to any portion of your organization that you define.
They are useful to restrict administrative scope in organizations made up of independent divisions. Examples can be Universities, Government institutions, international companies, etc.
To use them, you need Azure Active Directory Premium license for each administrative unit admin, and at least Azure Active Directory Free licenses for the members.
The administrator, that will create them, work with users and groups, and assign scoped administrator roles to other users must be Global Administrator or a Privileged Role Administrator.
More info: Azure Active Directory Premium
Planning and Managing Azure AD Administrative Units
You can use administrative units to logically group Azure AD resources. An organization whose IT department is scattered (locally or globally) would create these units that define relevant geographical boundaries. Another scenario would be in case we have sub organization structure with some form of semi autonomy. The Administrative Units will represent individual entity – sub organization.
Administrative units are a common way to define structure across Microsoft 365 services. Scoped administrators can use Azure AD or Microsoft 365 portal for basic management of users and groups, as well as PowerShell, Microsoft Graph for more advanced operations.
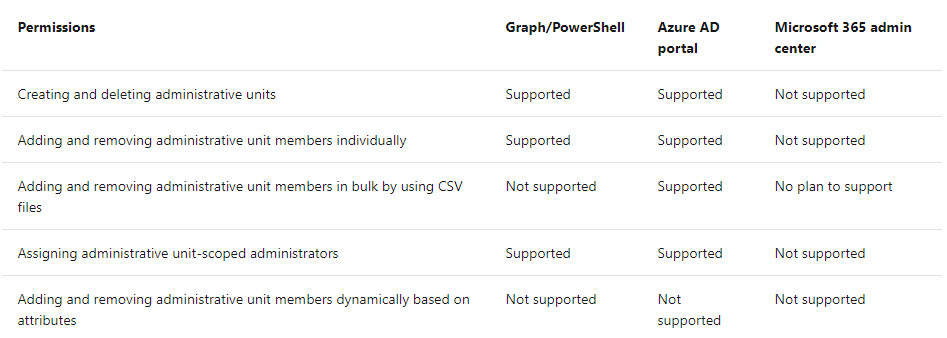
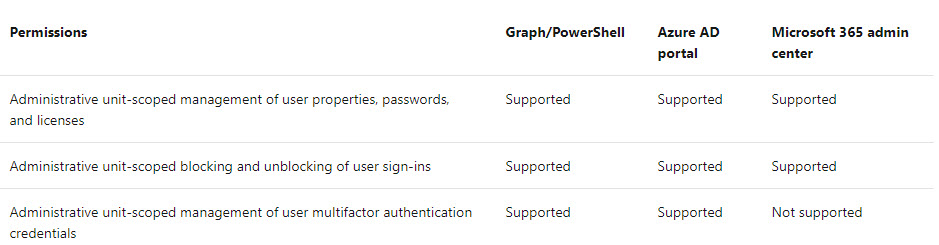
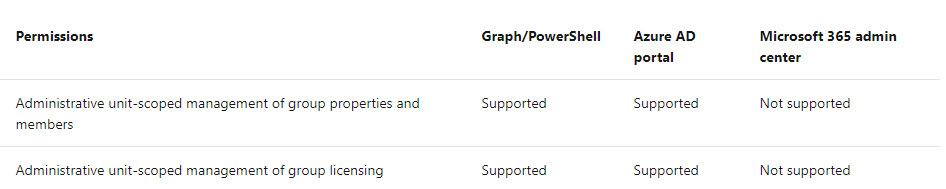
As far as the supported scenarios goes, its like this:
Working with Azure AD Administrative Units
Azure Administrative units can be created in the Azure Portal, with PowerShell, or Microsoft Graph. For Cloud Shell, you will need active Azure Subscription.
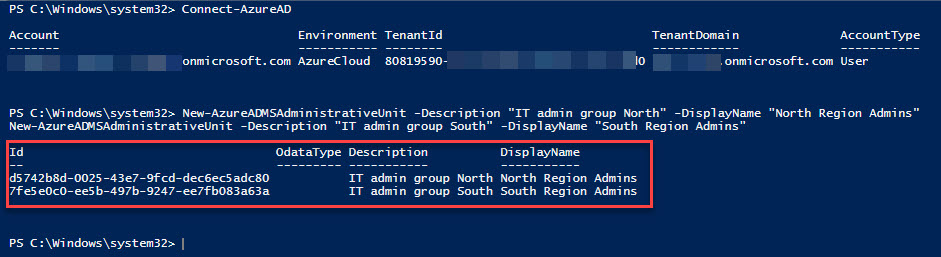
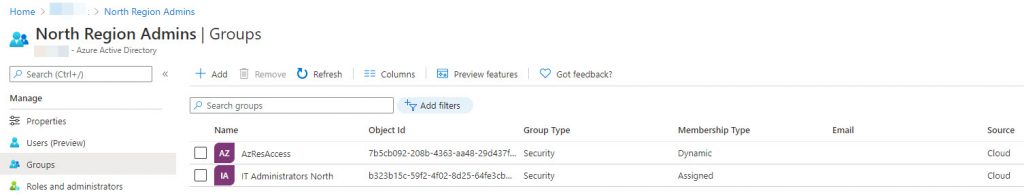
New-AzureADMSAdministrativeUnit -Description "IT admin group North" -DisplayName "North Region Admins"
New-AzureADMSAdministrativeUnit -Description "IT admin group South" -DisplayName "South Region Admins"
These commands will create two Administrative Units – IT Admin group North and IT Admin group North South (as shown on the picture below).
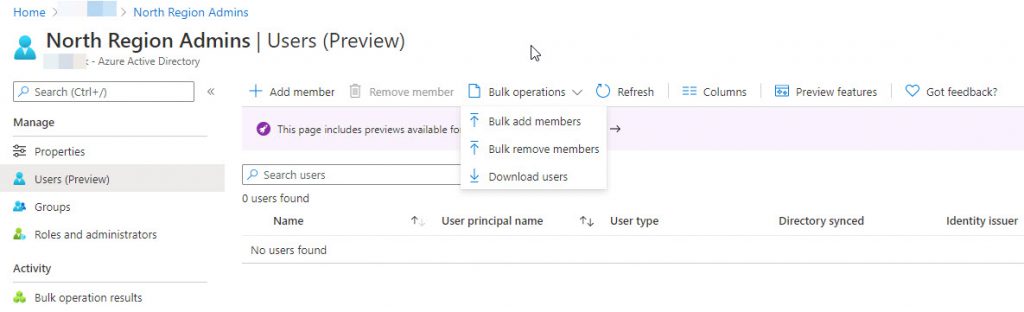
Now you can add users and/or groups, as part of the administrative unit, and then assign administrative roles. There is possibility to download CSV file and perform bulk operations.
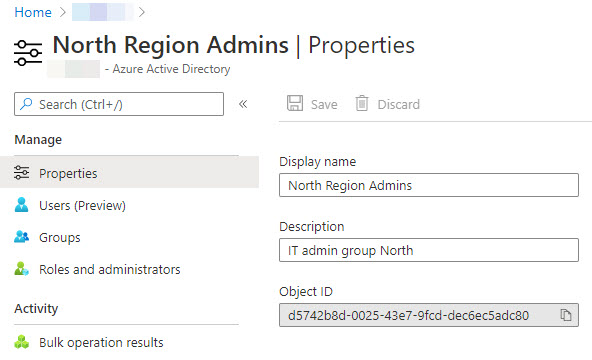
Out of the group properties, you can change the name and description. Object ID is unique and assigned at the time of creation.
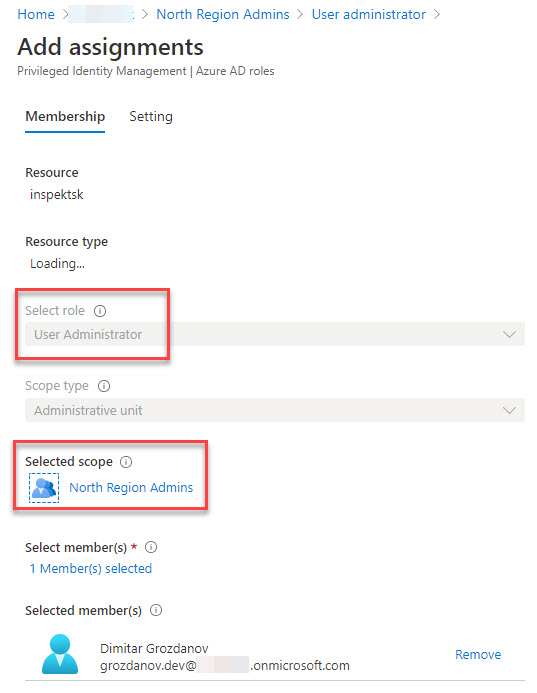
Once you assign the users and/or groups, as part of the Administrative Unit, you can assign roles to specific objects.
Role assignment functions same as Privileged Identity Management process. Based on selected Role, the user or group we Add assignments. In short, the scope is fixed to the Administrative unit selected (North Region Admins).
More info: Azure Active Directory Privileged Identity Management
Security principals, that can be assigned to a role within an administrative unit scope, are:
- Users
- Role-assignable cloud groups (preview)
- Service Principal Name (SPN)
Adding a group, does not mean that its members will be assigned a role automatically. Security groups themselves can be members of resource scopes. This brings those groups within the management scope of the user administrators for that Administrative Unit.
The Administrative units will work only for Azure AD objects, not B2C organizations.
Some features like Search groups and members, for which you can opt-in. More information can be found on the link.
Conclusion
This feature is definite win, in improving the security and administrative operations within a Azure AD tenant, combined with Microsoft 365 services
It helps distributed organizations assign appropriate roles to group of resources (users or groups), bound within specific administrative roles.
For additional information, visit the Microsoft Doc page.


Be the first to comment